I’ll start of by saying that I really love Teams, I do, BUT there is definitely room for improvement!
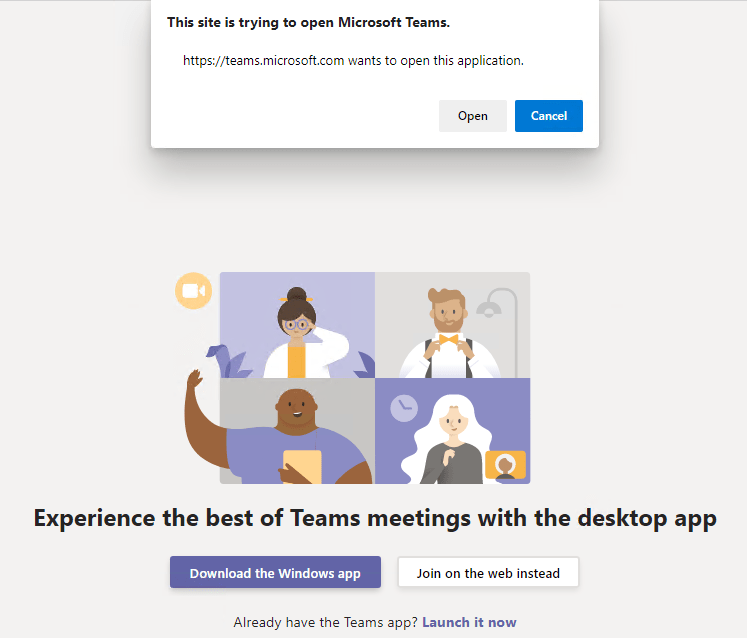
One of the things that really annoyed me lately is when joining an online meeting, the default web browser opens up and you need to click the “Open” button in the popup…. Why Microsoft….. Just Why??
Luckily (For you😁) it annoyed me enough to do some research and figure out how to get around it. Unfortunately I cant suppress the opening of the web browser, but I can get it to open the Teams app automatically 👍
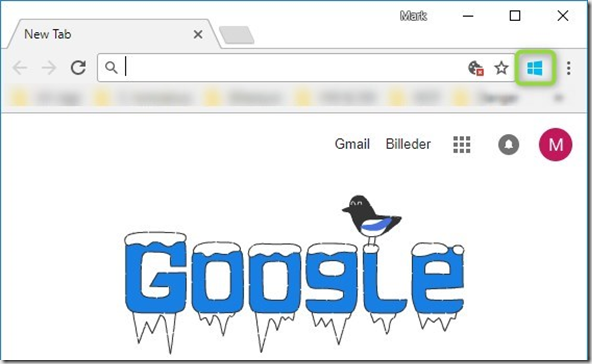
So here we go. Oh, and by the way, this guide will work with Google Chrome and Edge Chromium.
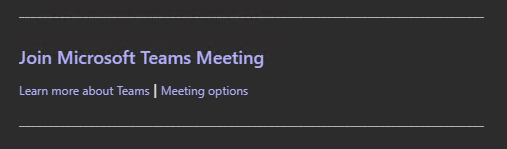
So you get an invite to a Teams meeting, and when you want to join, you click the “Join Microsoft Teams Meeting”
It opens your web browser, and that box, where you have to press “Open” (If you have the desktop app installed),
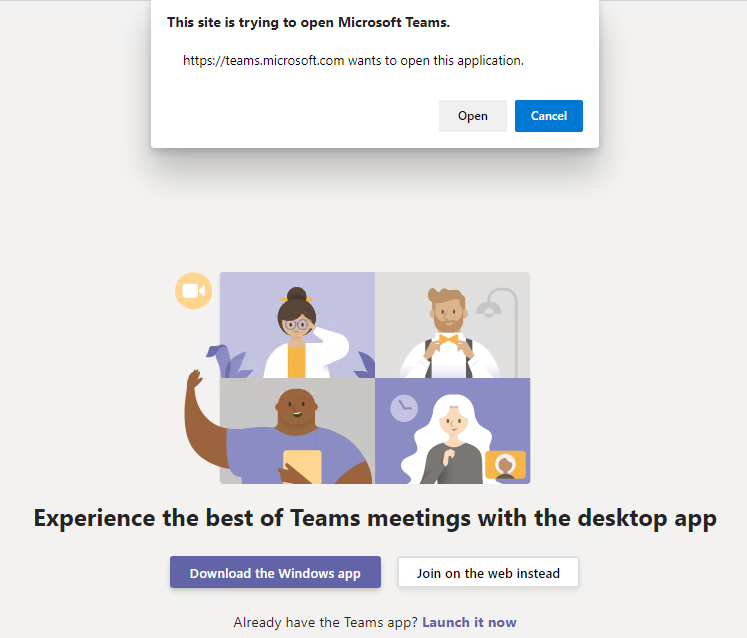
it launches you’re Teams app, and you’re ready to go. But why? Why not just open you’re Teams app right away?
Here is how in Edge Chromium
Open your registry and navigate to
[HKEY_CURRENT_USER\Software\Policies\Microsoft
Now, most likely you don’t have much in there, so you need to add the following key’s
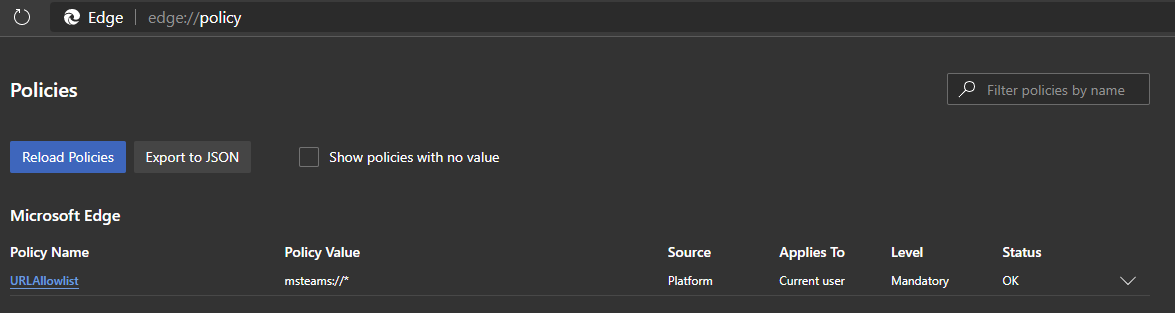
HKEY_CURRENT_USER\Software\Policies\Microsoft\Edge\URLAllowlist
Now add a new STRING value, name it 1, open it up and add the value
msteams://*
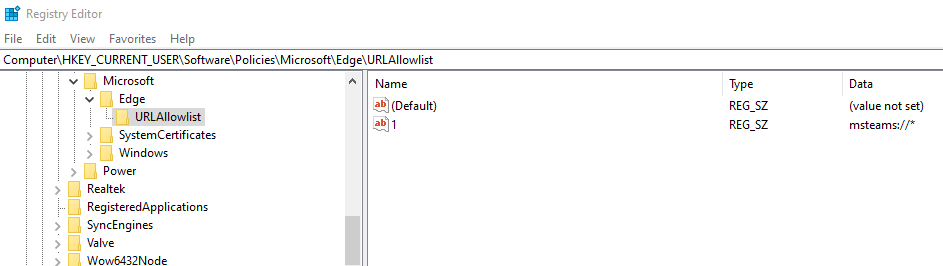
and that’s it😳, from now on when you click the “Join Microsoft Teams Meeting”, it opens your default browser and then the Teams meeting👍
If you want to do it with a Commandline, this should do it (Remember to run CMD as Administrator 😉)
REG ADD HKCU\Software\Policies\Microsoft\Edge\URLAllowlist /v “1” /d “msteams://*” /t REG_SZ
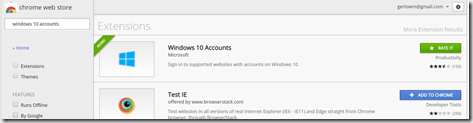
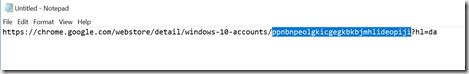
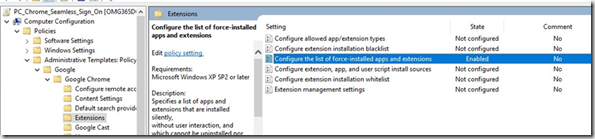
Here is how in Google Chrome
HKEY_CURRENT_USER\Software\Policies\Google\Chrome\URLWhitelist
Now add a new STRING value, name it 1, open it up and add the value
msteams://*
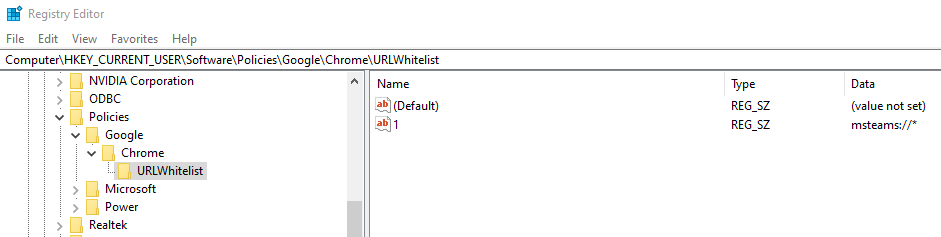
Again, if you want to do it with a Commandline, this should do it (Remember to run CMD as Administrator 😉)
REG ADD HKCU\Software\Policies\Google\Chrome\URLWhitelist /v “1” /d “msteams://*” /t REG_SZ
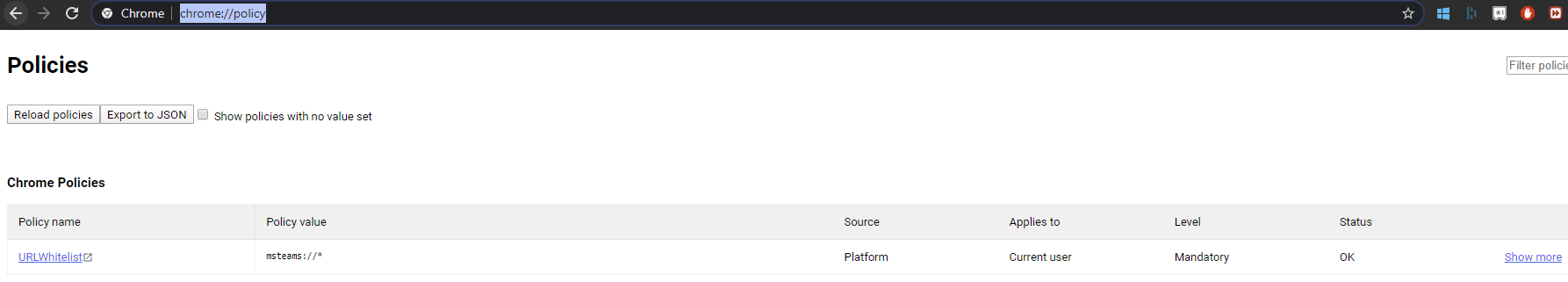
You can double check that the policy works correctly, if you open Google Chrome or Edge Chromium and go to:
Or for Edge
Happy Teaming 😊


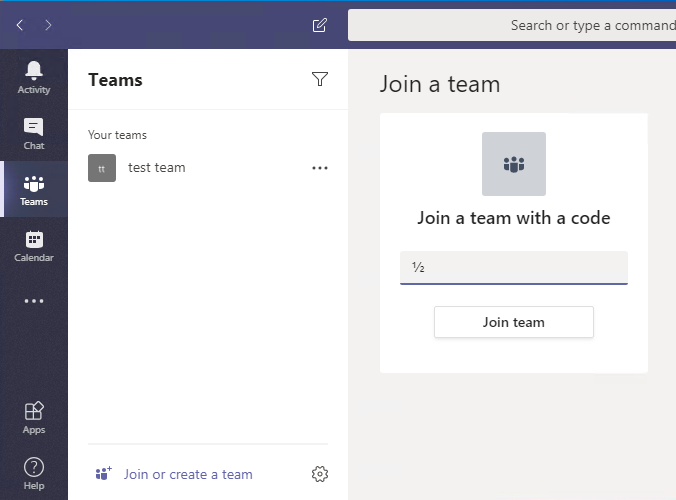
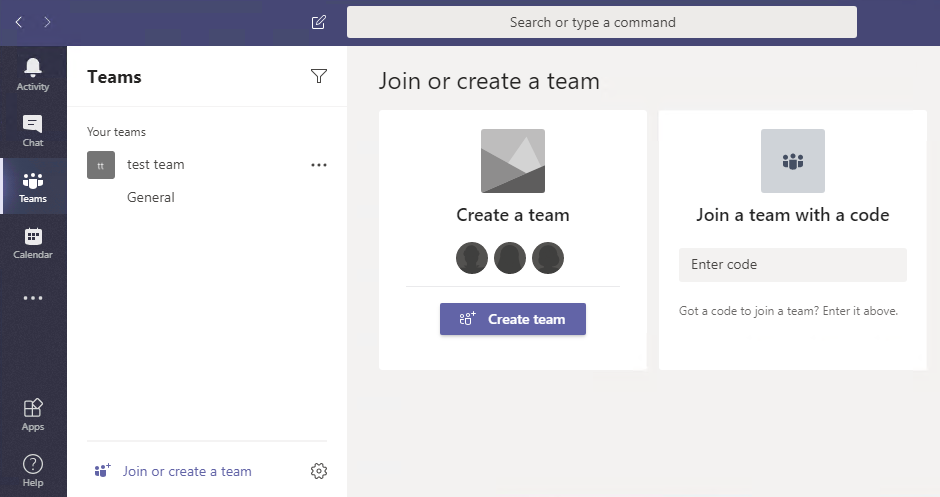
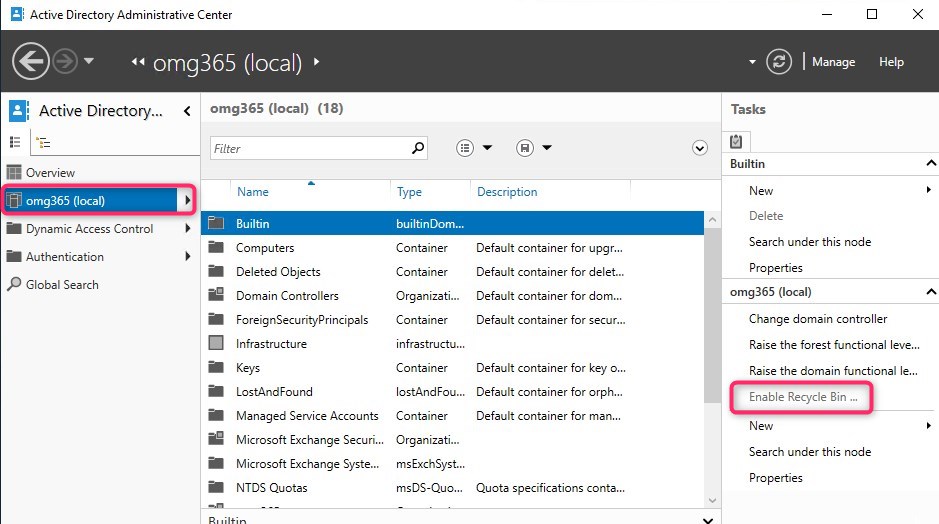
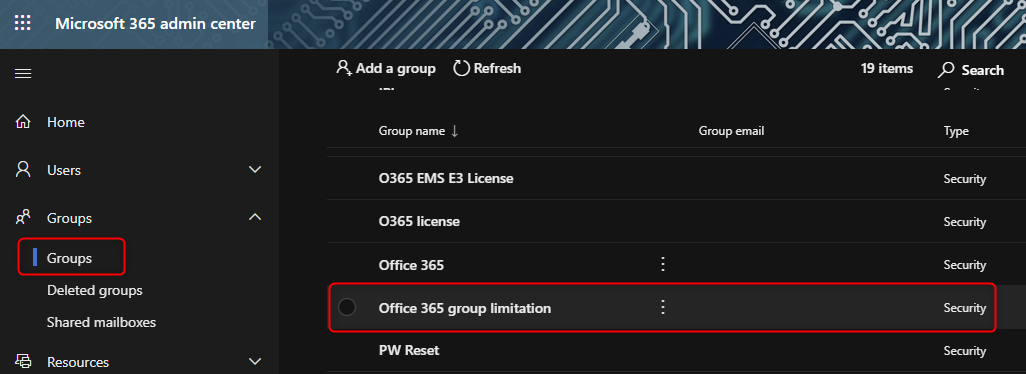 In my Example I created the group “Office 365 group limitation” Copy the below PowerShell script to your favorite editor, like Notepad, PowerShell ISE or Visual Studio Code. Name the script how you like, I kept it like MS suggested, GroupCreators.ps1
In my Example I created the group “Office 365 group limitation” Copy the below PowerShell script to your favorite editor, like Notepad, PowerShell ISE or Visual Studio Code. Name the script how you like, I kept it like MS suggested, GroupCreators.ps1