Accidents happen, we are only human and sometimes we accidently delete something that we shouldnt have. In most cases its no big deal, we can restore ![]() . When it comes to Active Directory, it actually can be an issue. AD restores can be a nightmare (in my humble oppinion, anyways).
. When it comes to Active Directory, it actually can be an issue. AD restores can be a nightmare (in my humble oppinion, anyways).
On a quick sidenote, enable AD recycle Bin, it can really save you some time.
Open Active Directory Administrative Center
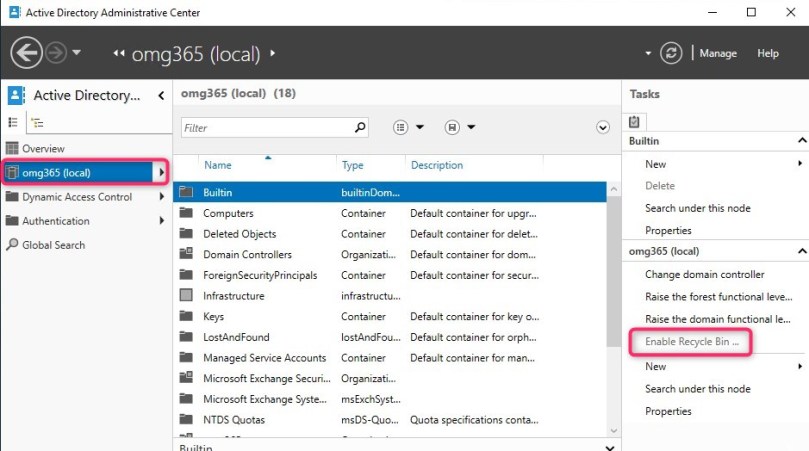
After enabling it, you can’t disable it (but why would you?)
BUT, in this case we “act” like, we havent enabled it ![]()
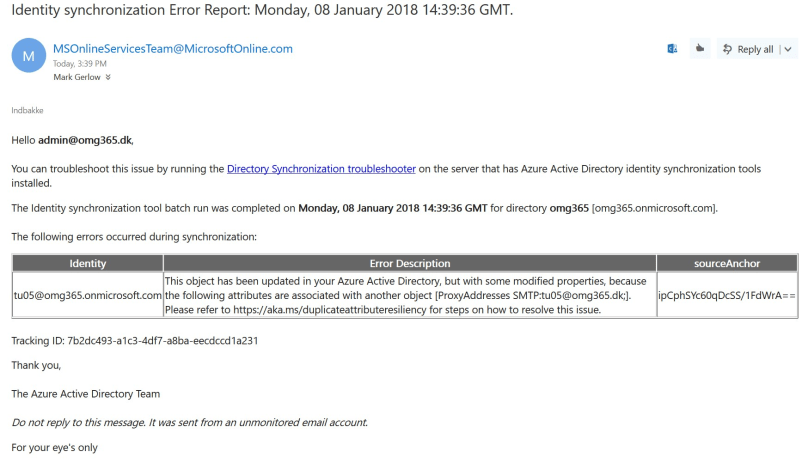
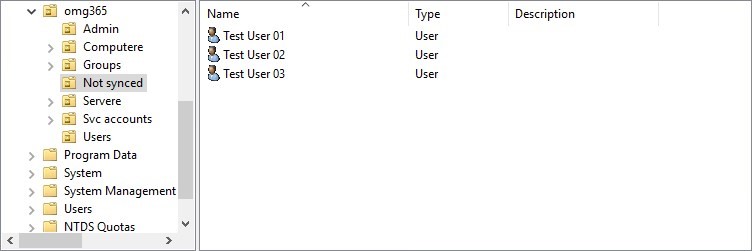
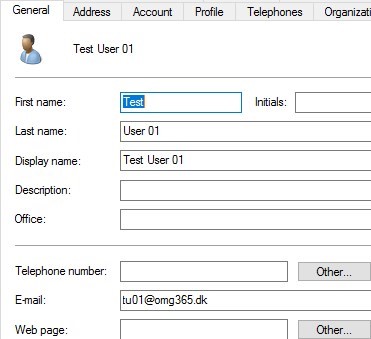
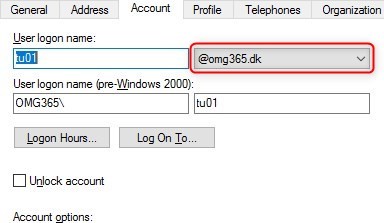
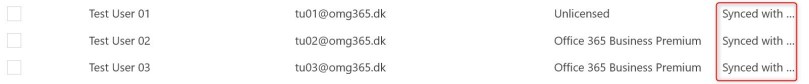
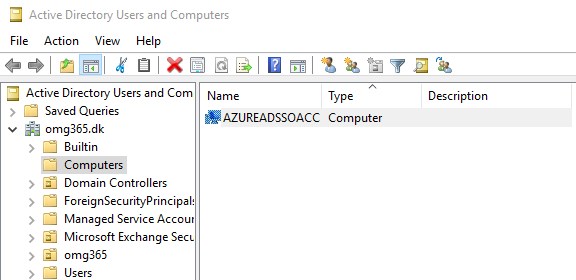
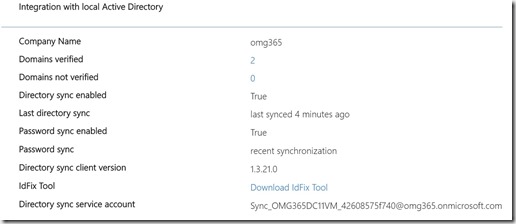
So somebody accidently deleted the AZUREADSSOACC computer account . This is the “virtual” computer account, used with Azure AADConnect when you enable SSO. (You can read more about it in a previous articel HERE.
Normally its placed In the Computers container
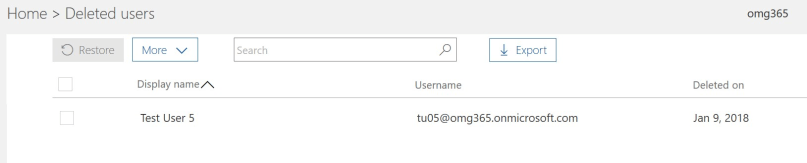
But, in this case we deleted it ( And just to prove to you, that I’m not cheating  )
)

It’s gone![]()
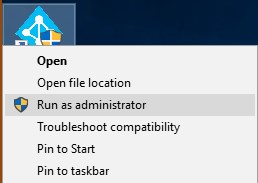
First you need to log on the computer on which you have AADConnect running.
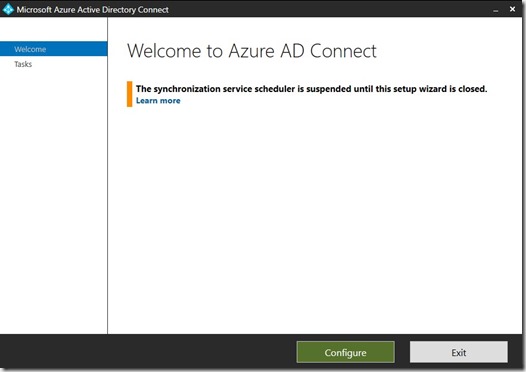
Right click, and choose run as Admin (If you have UAC enabled, click yes ![]() ) on the “Azure AD Connect” icon, placed, must likly on your desktop (Thats default)
) on the “Azure AD Connect” icon, placed, must likly on your desktop (Thats default)

Click “Configure”
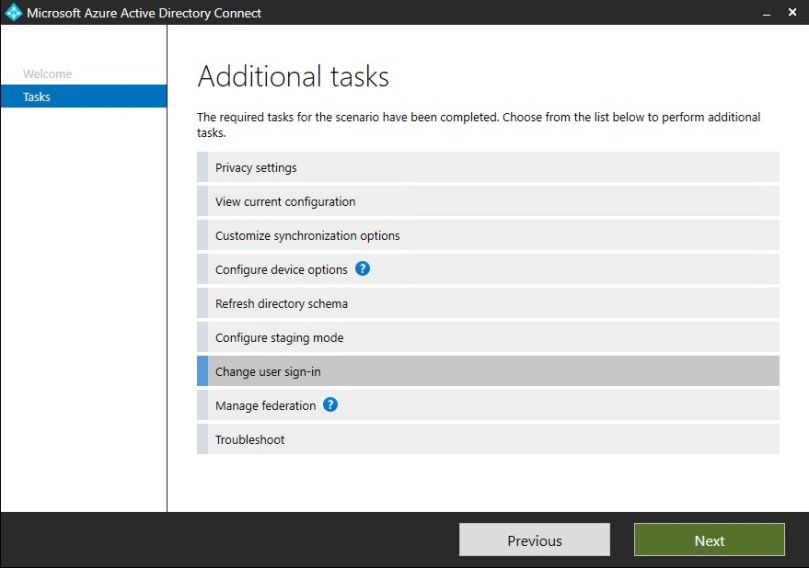
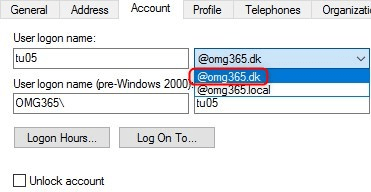
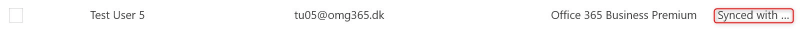
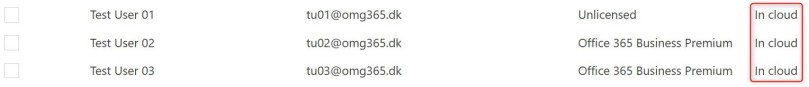
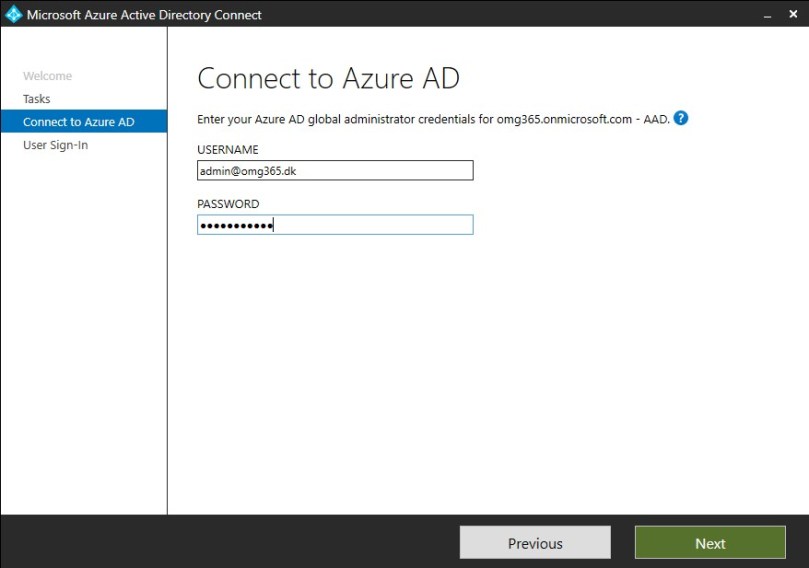
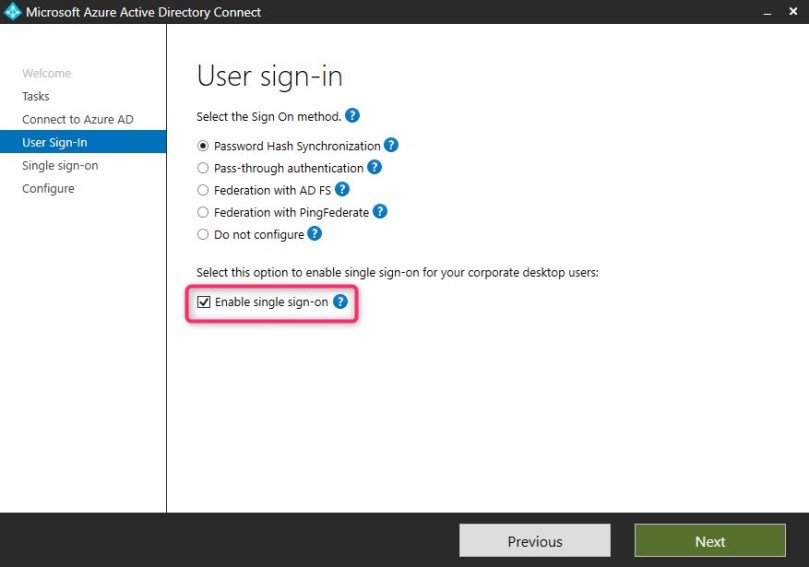
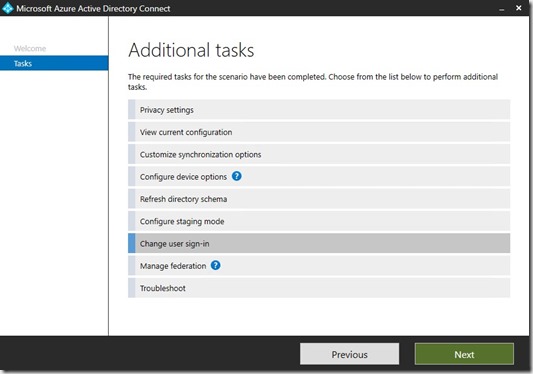
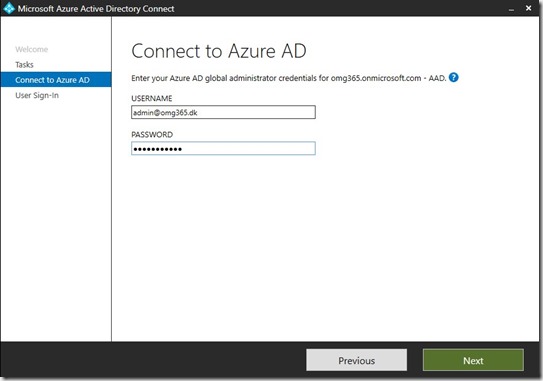
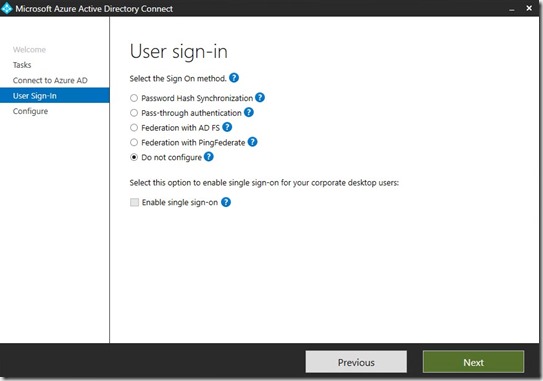
Choose “Change user sign-in”, and click next. Logon with your Office 365 Global Admin account
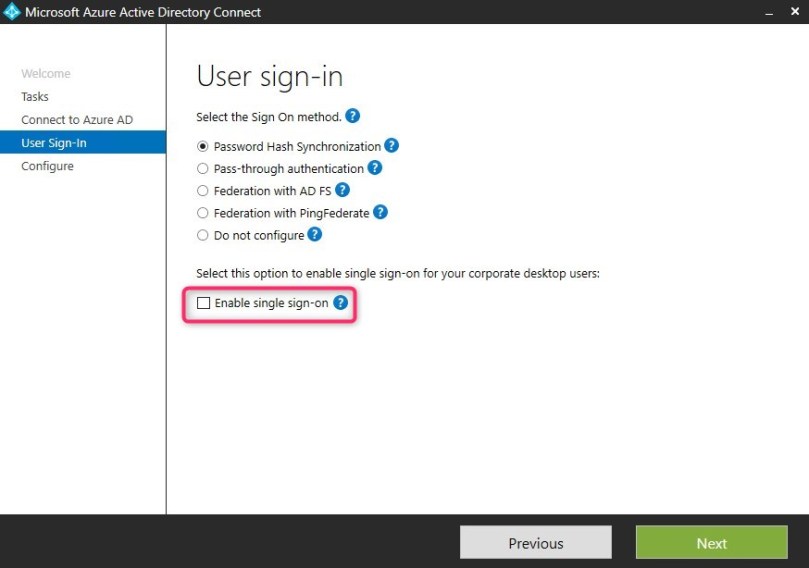
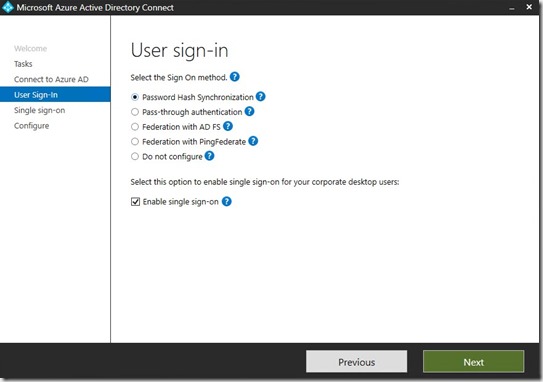
Remove the option for “Enable single sign-on” and click next
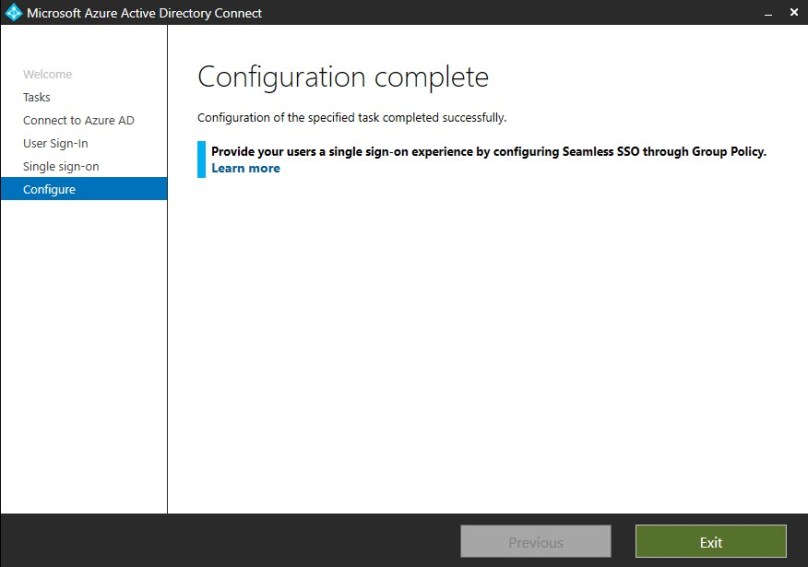
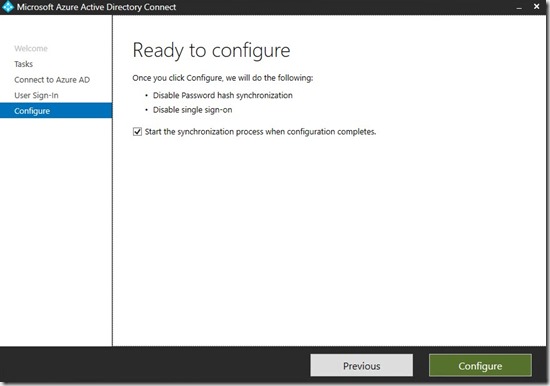
And then, Configure
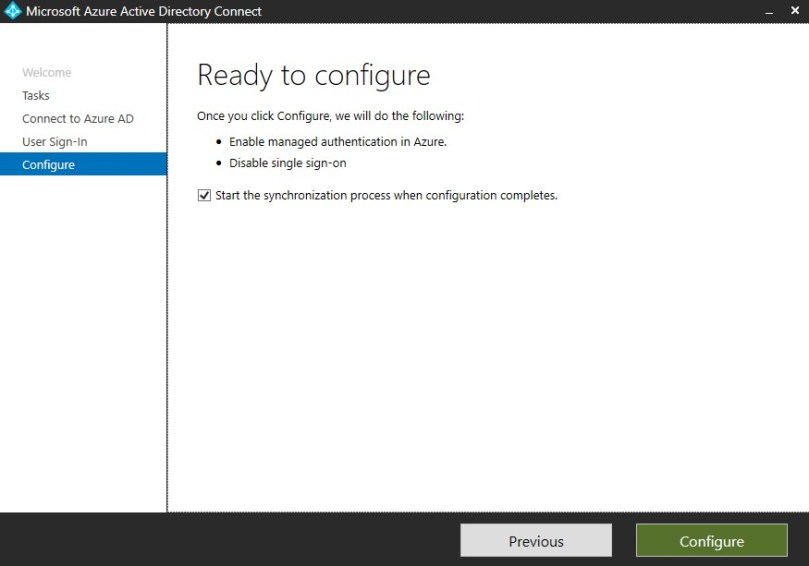
Now, if the next screenshot is what you get, you are got to go![]() . If it comes with a warning, saying something like “Single sign-on could not be disabled”, have no fear, it did for me when I did some test the first time. Run the wizard to the end, wait 5-10 min. and try again. You should end up with it being succesfully disabled.
. If it comes with a warning, saying something like “Single sign-on could not be disabled”, have no fear, it did for me when I did some test the first time. Run the wizard to the end, wait 5-10 min. and try again. You should end up with it being succesfully disabled.
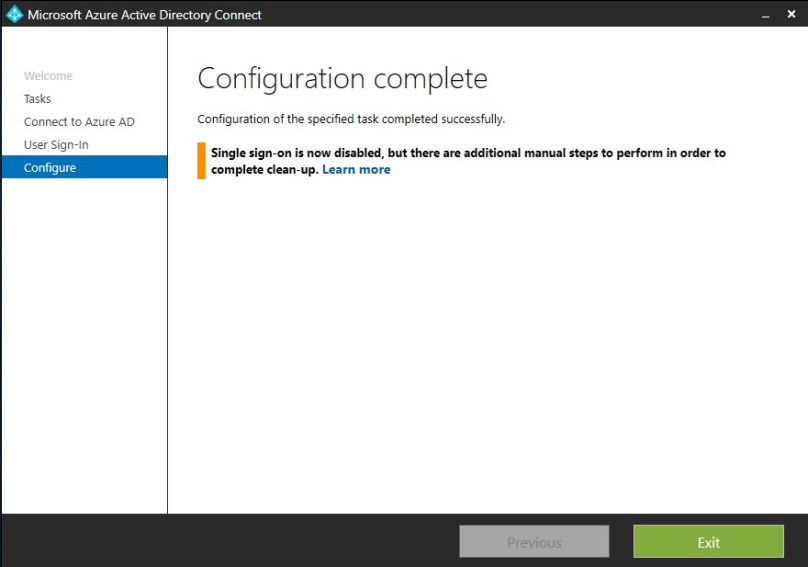
Status: For now, we have diabled SSO. Now we need to enable it again, because its an awesome feature and we really want it……
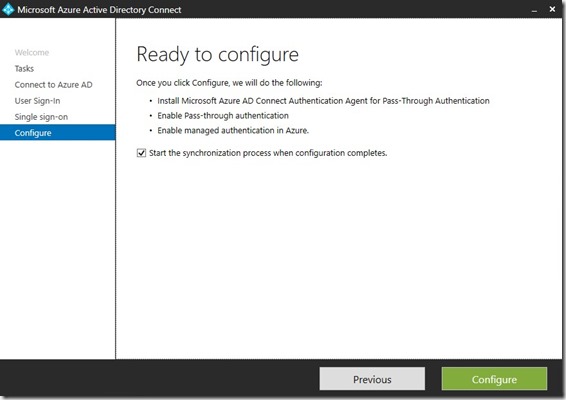
Run the Wizard again (As an admin), and make sure you set the tick (or what ever you call it) in “Enable single sign-on”
Click next – In the “Enter credentials” box, you need to provide your local Domain Admin

Click OK, and next

Click “Configure” and let the wizard do its magic![]()
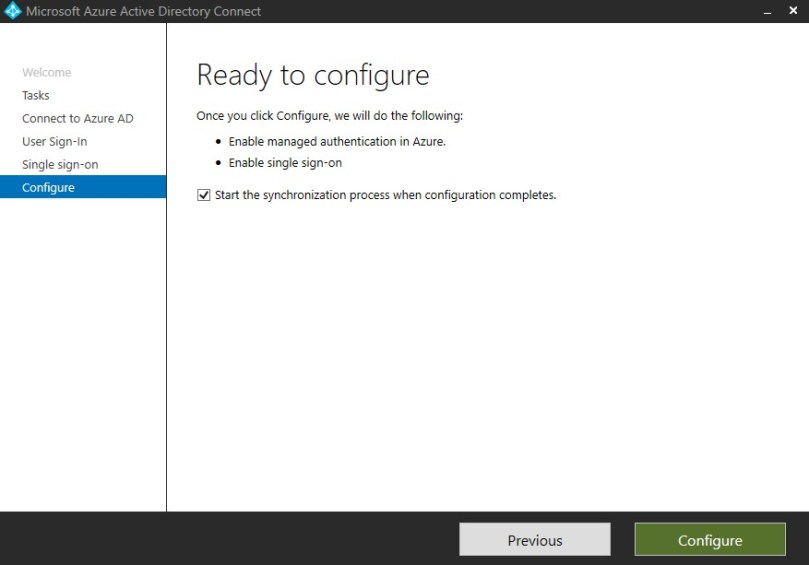
Dont be alarmed, if it throws an error, it did for me a couple of times, just hit retry.
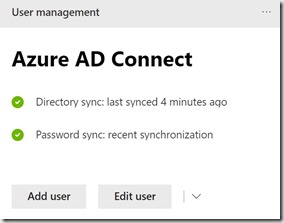
Yay…success… and look, AZUREADSSOACC is back where it belongs in AD ![]()
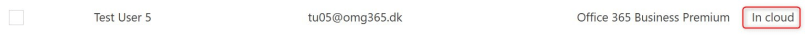
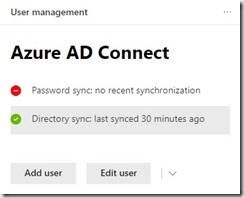
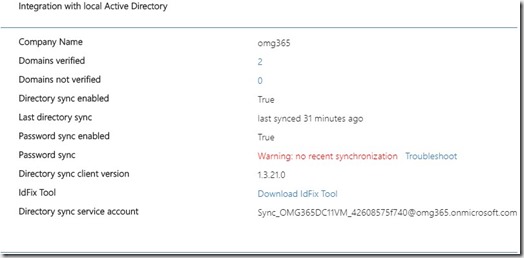
Give it time to run a sync (or force one with PowerShell Start-ADSyncSyncCycle -PolicyType Delta ), but eventually it will sync back up, and work like it did before.
Happy Clouding ![]()










 )
)


 ), you need to add some URL’s to the local intranet zone. Preferably done by GPO. These are the 2 addresses you need to add:
), you need to add some URL’s to the local intranet zone. Preferably done by GPO. These are the 2 addresses you need to add:





 , or just go to
, or just go to  . I will list my view on pros and cons here.
. I will list my view on pros and cons here.